TSCM Bug Sweeps

Most modern businesses operate digitally to one extent or another and many these days are exclusively digital.
You might run an online mail order business where your online orders are fulfilled by a drop shipping partner, which means you don’t have to hold any stock – you just join the dots, acting as a middle man between the buyer and supplier. Then again, you might run a more traditional business that relies on Information Technology (IT) networks and computers to keep customer records, take stock and manage various aspects of the customer journey.
No matter what business you are in, a security breach could easily result in financial disaster for your company. You might have your customer data stolen, maybe suffer an internal security breach that prevents your staff from doing their jobs properly. Or an entire system could be so badly hacked or infiltrated that it comes to a complete halt.
We know how stressful and worrying it can be for those managing and maintaining IT security, when their company’s success is reliant on computers and computer networks. We also know that being a victim of any type of security breach will always be embarrassing, most often be financially damaging and will occasionally be completely disastrous.
Have you factored in TSCM?
Prudent businesses recognise the importance of Technical Surveillance Counter-Measures (TSCM) and implement a company TCSM programme. If you operate a network or computer system, especially if you store sensitive information or customer information such as credit card, bank account and personal details – a TSCM sweep should take place quarterly to six monthly.
Imagine your organisation suffers a hostile takeover or is involved in a complex legal case. You want to be certain that confidential undisclosed information can’t be accessed remotely. System security can influence your business’ very survival.
In many cases where sensitive business information has been lost, the loss can be traced back to a poor internal security policy, rather than an actual act of targeted espionage. Even so, whether you believe the root cause of your security failure to be an in-house matter or the result of external penetration, it is important to have a professional investigator assess the cause of the breach.
As part of that investigation, we conduct a full security policy review where your system is screened, tested and scanned for additional gaps in your IT defences.


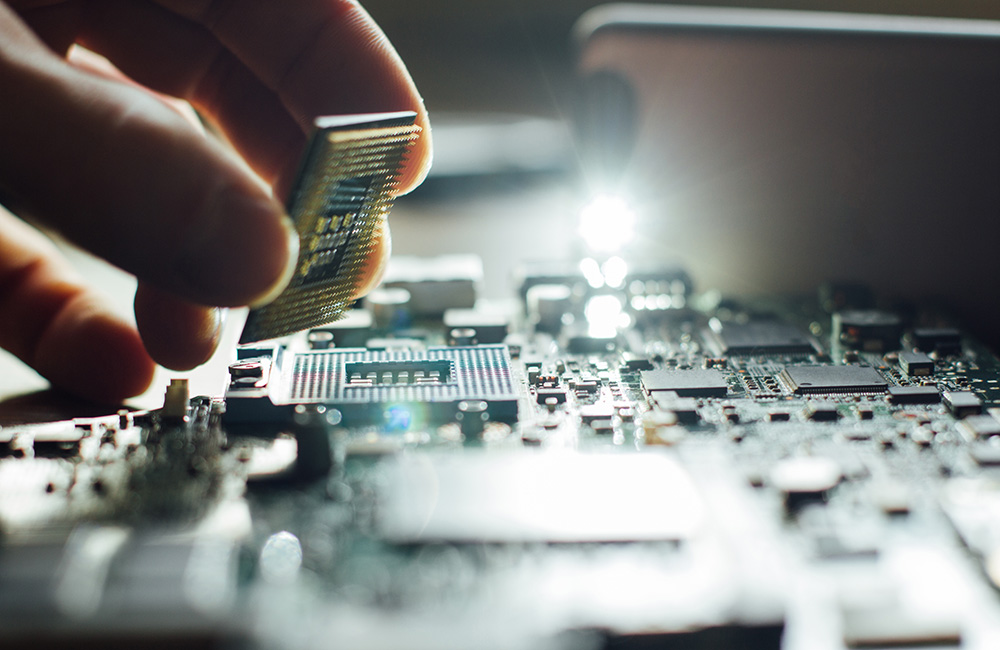
Check your computers haven't been turned into listening devices
Did you know your company’s computers can be used to eavesdrop on office discussions, meetings and employee phone conversations?
Your computer hardware is just as, if not more, vulnerable from an external attack as your network or computer system. An office laptop or PC can easily be transformed into a listening device. It doesn’t even require a qualified technician with specialist skills to carry out the transformation, it just takes someone with a degree of computer literacy, someone who can gain access your computer.
You might also be unaware that an IT network and computer system TSCM sweep doesn’t usually include searching hardware on your premises or outside your buildings, equipment used by your employees at home, in a vehicle or taken out to external meetings. Whether or not your business has an internal IT team, it is important to have key employees’ electronic machinery regularly checked for devices hidden inside.
Why partner with us?
We know computers are the perfect place to hide a hard-wired device, which is why we always advise our customers to employ a professional and qualified IT expert to carry out a thorough physical inspection of their equipment. Otherwise someone without the right expertise could very easily miss a threat hidden in plain sight.
Arrange a specialist sweep of your IT networks and computer systems
A regular TSCM sweep should be part of your ongoing counter-espionage policy, not something you do in isolation. We at Eagle View Investigations treat every enquiry with the utmost confidentiality, so if you would like to know more about Technical Surveillance Counter Measures, please get in touch for a discreet informal discussion.


